Base64 encryption is a lie
You were told or you thought that the Base64 is an encryption algorithm? Achtung! This is not only erroneous, but also very dangerous, because Base64 is just an encoding algorithm that does not protect sensitive data in any way.
Remember!!! Everyone can decode a Base64 string just as easily as you encoded it. Some can decode it simply using a regular pen and paper.
Base64 is like a foreign language. Even if you do not speak it, you can use an online decoder to “translate” Base64 to text. Technically, it’s the same as translating Chinese into English using Google Translate. The only difference is that Base64 is much simpler and, unlike the machine translation, it never fails. Therefore, you cannot use Base64 to hide or protect sensitive information, such as passwords, tokens, private keys, or any kind of confidential information.
I published this article because according to a recent “Password-Storage Field Study” it turned out that 8 of 43 freelancers have chosen Base64 to “encrypt” passwords. It scares me that so many developers think that “Base64 is very tough to decrypt” or that “Base64 encoded passwords are considered encrypted because they are not stored as plaintext”. In addition, researchers discovered that many developers do not understand the difference between encoding, hashing, and encryption. So, let’s briefly describe each of them.
-
Encoding converts data into a “reliable” format to ensure that it will not be damaged during transmission. Encoding algorithms (such as Base64, Morse code, Punycode, URL encoding) are very simple and come down to the substitution of some characters by others. To get the original data it is enough just to reverse the substitution process.
-
Encryption “hides” data by protecting it with a password so that data can be viewed only by those who know the password. Encryption algorithms (such as AES, Blowfish, DES, Twofish) are designed to protect secret data and ensure that even if encrypted data is stolen, it will not be accessible to unauthorized persons, since they need the password to decrypt it.
- Hashing computes a unique “identifier” for the data provided, which most often is used to check the data integrity. Hash algorithms (such as MD5, RIPEMD-160, SHA-512, Whirlpool) are one-way functions that do not have a reversible algorithm, therefore, no one can get the original data only on the basis of the provided hash. The only way to guess original data is to crack the hash using brute-force.
I know, these definitions are too vague, but the idea is to show the difference between them. That’s why I strongly recommend you to go deeper and read at least the following Wikipedia articles:
If you’re a regular user looking for a Base64 encryption tool, check out the Base64 encoder and, please, never mention that erroneous words. If you are a developer, don’t forget that security is paramount and always pay more attention to it. If you are a professional who knows how to improve this article, feel free to ping me. If you find this article useful and want to make the web a bit more secure — spread the word and share the knowledge. If you know an instructive story about Base64 encryption, please don’t be selfish :)
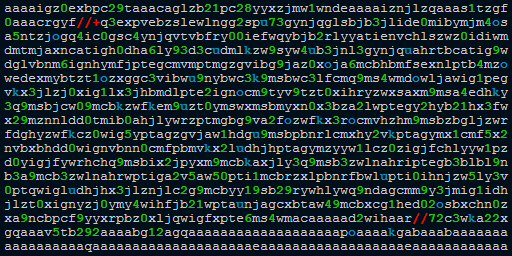 What is "aaaaigz0...my4xmda="?
What is "aaaaigz0...my4xmda="?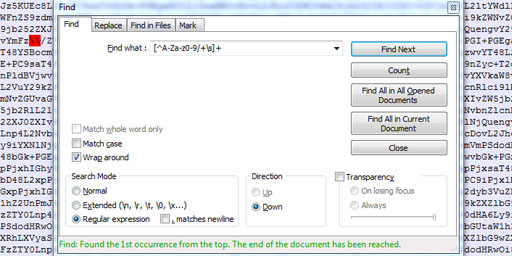 Validate Base64 using Notepad++
Validate Base64 using Notepad++ Launched the Base64 Repair Tool
Launched the Base64 Repair Tool
Comments (37)
I hope you enjoy this discussion. In any case, I ask you to join it.
https://github.com/base64encrypted/php_base64encrypted
Is it encrypted or encoded?
As for the algorithm, I did not analyze it, but even if it is an encryption algorithm I would not trust it.
https://sebsauvage.net/paste/?36a4754464ed1d34#tucc+ZxbYliC/LA+tqEvils2sUuhDQr6ELGoizVD89A=
By the way, do you know any details about php_base64encrypted? Maybe some in-depth reviews or thoughts?
A better idea would probably be, to "encrypt" data using Base58 which looks a lot like Base64 :D
Grazie ☺️
hT2fnEK8WqptVGWLhT2fnEK8WqptVGWtLF83W5S3EVU>dHet
HLY_>W3
JG=AJ54 CYh9avte4ggVt.
9UHOU_EQ8&dETW9q>erT4K9_IS?GrGJ?
dBRw9
E
9dR'CTCKétK:vaGZ88tV2fEK=s8Wvu5VGW
t+OD5TNV8dEytU&>EVvEX4JF
G5S!CV:aHp et T7Y,
9W0JGaQ5aEYB99au894/TtM.9UR?
JqrGJ8aHdE>609eCT4NL9ILOGtEGItd_W0G;
ZK9
Do you think I could post it on the web for an answer ?
Thanxx anyway for your nice site bro, you have a beautiful job^^
Newbee
V0VBVEhFUiBSRVBPUlQgMDYwMCBFTkdMSVNIIENIQU5ORUwgT1ZFUkNBU1QgV0lORCBORSAxMiBLUEggU0VBUyAyNSBETSBURU1QRVJBVFVSRSA5IERFR1JFRVMgSFVNSURJVFkgNTAgUENUIFZJU0lCSUxJVFkgMjAgS00=
WEATHER REPORT 0600 ENGLISH CHANNEL OVERCAST WIND NE 12 KPH SEAS 25 DM TEMPERATURE 9 DEGREES HUMIDITY 50 PCT VISIBILITY 20 KMreport
but...that might give us a clue?
hmm...oh! maybe it blew into the
reporters face who was giving the
report! i love how this site is both
logical and hilarious, i vote 10/10
If its not asking for a password to "encrypt" data, and you can do the reverse task,
then its not safe and anyone can decrypt this easily in 1 second.
To explain it better; base64 is a different base. Just like decimal (base10) and hexadecimal (base16).
If you convert the decimal number
28into hex it becomes1C.If you convert the hex number
1Cto decimal, it becomes28, again.This is what base64 does; decimal
28becomes base64b, and the other way around.to encrypt data,however,it cant encrypt
something alone. what i mean is,1. if you
take Base64 , 2. hand-convert it to letter-
place value in Base64,and finally,3. convert
the Base64 letter-place values to decimal,
the ascii that comes back will mostly be (bc of decimals rules)nonexistent
(a whitespace),or,not make any sense
(a punctuation,a symbol,or,both visually
and logically,nonsensically placed,or,even
completly incorrect letters) and,if you want
to make it endless pain and suffering all for
no point for certain types of hackers,make
whats encoded to Base64 not even the
password(i'm 90% sure this will make them
rage-quit at trying to decrypt the whole
thing).
(this ^ is here bc idk if the site adds this
automatically)
for those of you who are curious about
the in-depth process,this edit addresses
said process:
so the Decimal to ASCII conversion
rule is: anything from 0-32(in Decimal)
is nonexistent in ASCII.
While Base64's rule is: anything from
0-25 is a U-case letter(0=A [and so on]
,anything from
26-51 is L-case letter(26=a [and so on]
,52-61 is numeric(52=0 [and so on]),
(62-63=+-/
if you notice,Decimal can-if Base64 is
turned into place-value-cause a large
portion of data loss based on how
many characters have a place-value
within 32 (removing all U-case and from
a-g in L-case) making this a potent
form of encryption,
p.s:the more legit and less obvious that
it there is more complicated steps
involved,the more pain they have to go
through.
If the Scatman can do it, brother, so can you
I'm the Scatman
Ba-da-ba-da-ba-be bop-bop-bodda-bope
Bop-ba-bodda-bope
Be-bop-ba-bodda-bope, bop-ba-bodda
Ba-da-ba-da-ba-be bop-ba-bodda-bope
Bop-ba-bodda-bope
Be-bop-ba-bodda-bope, bop-ba-bodda-bope
Ski-bi-dibby-dib yo-da-dub-dub, yo-da-dub-dub
Ski-bi-dibby-dib yo-da-dub-dub, yo-da-dub-dub
Ski-bi-dibby-dib yo-da-dub-dub, yo-da-dub-dub
Ski-bi-dibby-dib yo-da-dub-dub, yo-da-dub-dub
For example in earlier protocols symbols from #0 to #27 was special symbols, and if they appear in data stream - it was a command, like #26 - is End_Of_File
oh,nice joke...& no i didnt get hacked sweeet little perceptive 1...& no...im not saying how i didnt...good eye tho...I mean you are right but you are just understanding 1/2 of it..
However...its not very known about so idt i'll say it
Another thing i might say even though it is off-topic is i've learned a way to use bin data shifts and compression as a way to encode and heavily obfuscate [and possibly reversibly hash]
smthn with this encoding+
Compression method,mostly server side encodable,but the 3rd step requires human intervention to Complete it and move on
Through the rest of the steps (at least i think?[yep,nothing exists that can quickly shift all of your hex data to the same lvl as the lower output]), heres the encoding pattern,mainly meant for data compression but can reversibly hash data (if the bin key is not given publically) aswell
Mp3/mp4,etc. > B64 > B32-36 > custom Beacon > Hexadecimal > subtract lower bacon hex value from all Hex data > remove spacing between 0's & 1's > decode to binary
This will compress the string to 1/8th of its size (or more based off of your bin types bit-size choice) and is exeptionally lightwheight for storing things in a .txt file
And bc this requires human intervention and a brain that knows whats here is compressed
And in this specific way...yeah...idt ppl would find that really easily,not to mention that they would have to be able to guess the binary decompression encoding type [although that's easy to brute-force] they'd still have no idea about the data size beyond the bin string and the repetitious hex wall they have,not to mention this allows you to compress even further when repeating the method for the bin key data too
an Interesting subject btw,i will say that Base64 has always had a few tricks up its sleeve with its case-sensitivity though,and have seen that used to obfuscate data before and found that one out as a novice,so,bit discouraging to think about but still is really powerful
Worth the chat,love
Livid eggplant lady(not a girl)
P.S,i meant step 4-5 dependant on if you use b36 or not_ __ ___ _ _ __ _____
| | \ \ / / \ | | |/ /|__ /
| | \ V /| \| | ' / / /
| |___| | | |\ | . \ / /_
|_____|_| |_| \_|_|\_\/____|
- LYNKZ INSTRUMENTS -
- TECHNICAL WORK IN PROGRESS -